 |
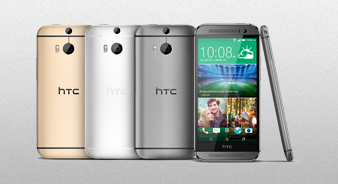
Клуб HTC One (m8)
для владельцев и любителей
|
| В | Главная | Характеристики | ПолныйВ обзор | Обсуждения | Информация | Отзывы |
|
Фото | Видео | Цены | Где купить |
View Blocked Websites At Work 'link' May 2026
View Blocked Websites At Work 'link' May 2026
For static informational pages, employees may use Google’s cached view or the Wayback Machine (archive.org) to retrieve a stored copy of a blocked site without directly accessing the live URL. This method only works for non-interactive content and cannot bypass login or real-time data restrictions.
Navigating Digital Restrictions: Methods, Ethics, and Risks of Accessing Blocked Websites at Work
Web-based proxies act as intermediaries: the user requests a blocked site via the proxy, which fetches the content and relays it back. Proxy sites are often short-lived, as IT departments quickly blacklist them. HTTPS proxies provide basic SSL encryption but may still expose request headers. view blocked websites at work
For technically adept users, establishing a Secure Shell (SSH) tunnel to a remote server can forward traffic through an encrypted channel. This method is harder for IT to detect than commercial VPNs but requires external server access and configuration.
From a virtue ethics standpoint, intentionally subverting employer controls while on work time violates trust and reciprocity. A utilitarian analysis might weigh the benefit of a few minutes of personal browsing against the cost of lost productivity and security incident response. Many organizations offer reasonable personal use policies (e.g., break-time allowances), making circumvention unnecessary. For static informational pages, employees may use Google’s
In the modern corporate environment, organizations often employ content filtering systems to restrict employee access to specific websites to enhance productivity, preserve bandwidth, and mitigate cybersecurity threats. Consequently, employees may seek methods to bypass these restrictions. This paper examines common techniques for viewing blocked websites at work—such as Virtual Private Networks (VPNs), proxy servers, and encrypted tools—while critically analyzing the ethical, legal, and security implications of such actions. The paper concludes that while technical circumvention is possible, employees must weigh these methods against corporate policy and potential professional consequences.
VPNs encrypt all internet traffic from an employee’s device and route it through a server external to the corporate network. To the workplace firewall, the traffic appears as a single encrypted stream, hiding the destination websites. Commercial VPNs (e.g., NordVPN, ExpressVPN) are popular. However, many corporate IT policies explicitly ban VPNs, and advanced firewalls can detect and block known VPN protocols. Proxy sites are often short-lived, as IT departments
Some basic filters block domain names (e.g., "www.facebook.com") but not the underlying IP address. If an employee obtains the IP address (e.g., via a ping from an external network), they can enter it directly. This method is rarely effective against modern deep packet inspection (DPI) firewalls, which analyze content regardless of addressing.
Как-то прям лего очень)
TheBrain, всё гениальное просто!
Как убрать root права скажыте пожалуста
Техподдержка утверждает, что "Вы просто добавили опцию в телефоне - для разработчиков в меню" и что "после этих действий аппарат не Root-ирован, и вообще root права не предоставлюется настройками телефона"
Отключить эту опцию нет возможности.
Спасибо
Но после этого всё равно праграмма гейм килер не запускается пишет нужны рут права что делать?
| HTC One (m8) - первый сайт о главном флагмане 2014 года |