Time needed: 5 minutes
Follow from Step 1 to Step 7 in order to create Opnet using Network Simulator projects. Quick guide to create Opnet Network Simulator. Reach us , if you want an customize Opnet simulator projects works for scholars.
- Need Software & Installation
1) OS: Windows 7[ultimatate -x86]
2) Processor:dual core or above
3) Ram :minimum 2GB
4) Riverbed opnet -17.5A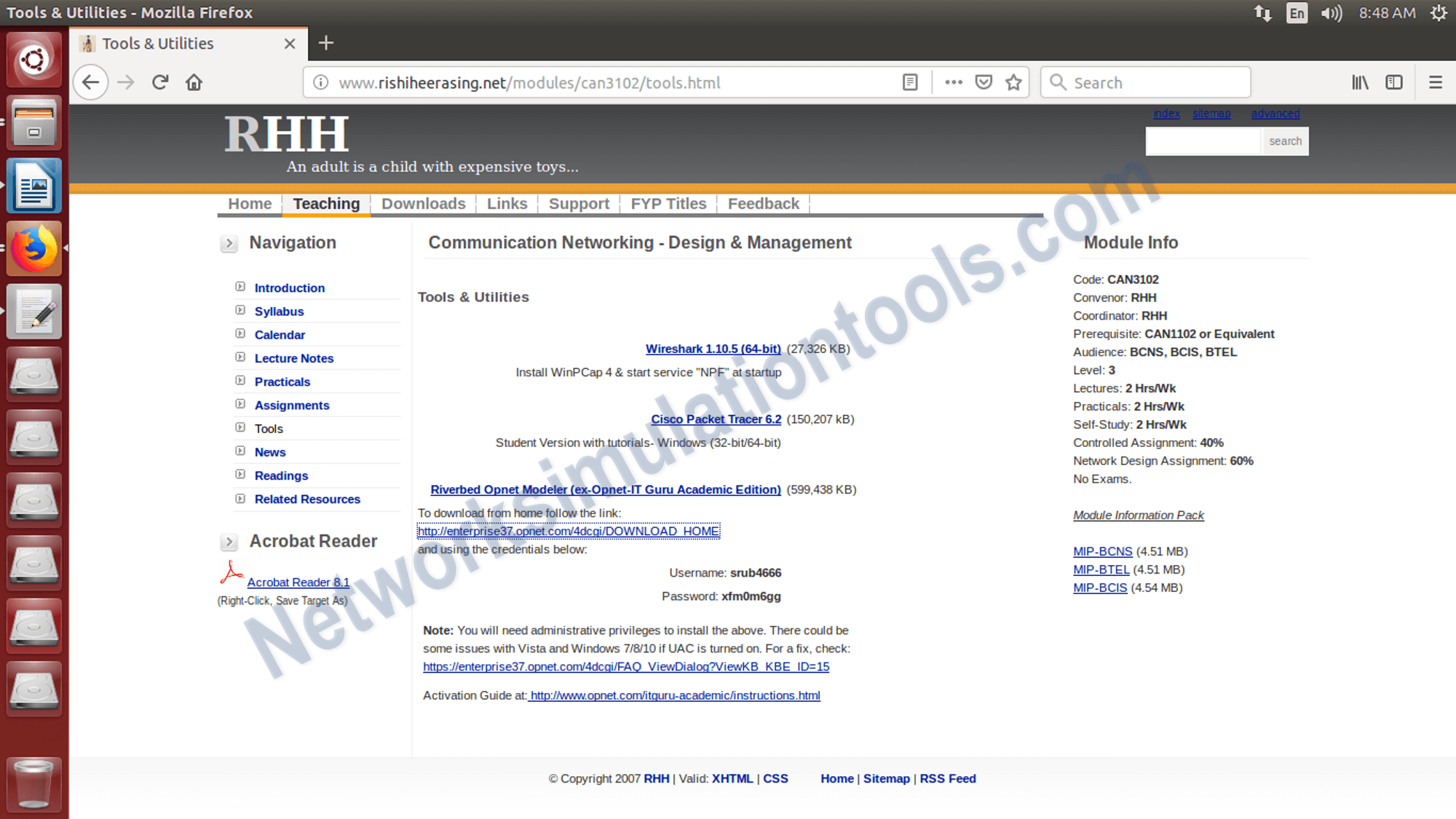
- Download and install Opnet
We can download the Riverbed opnet -17.5A from the following Link
http://www.rishiheerasing.net/modules/can3102/tools.html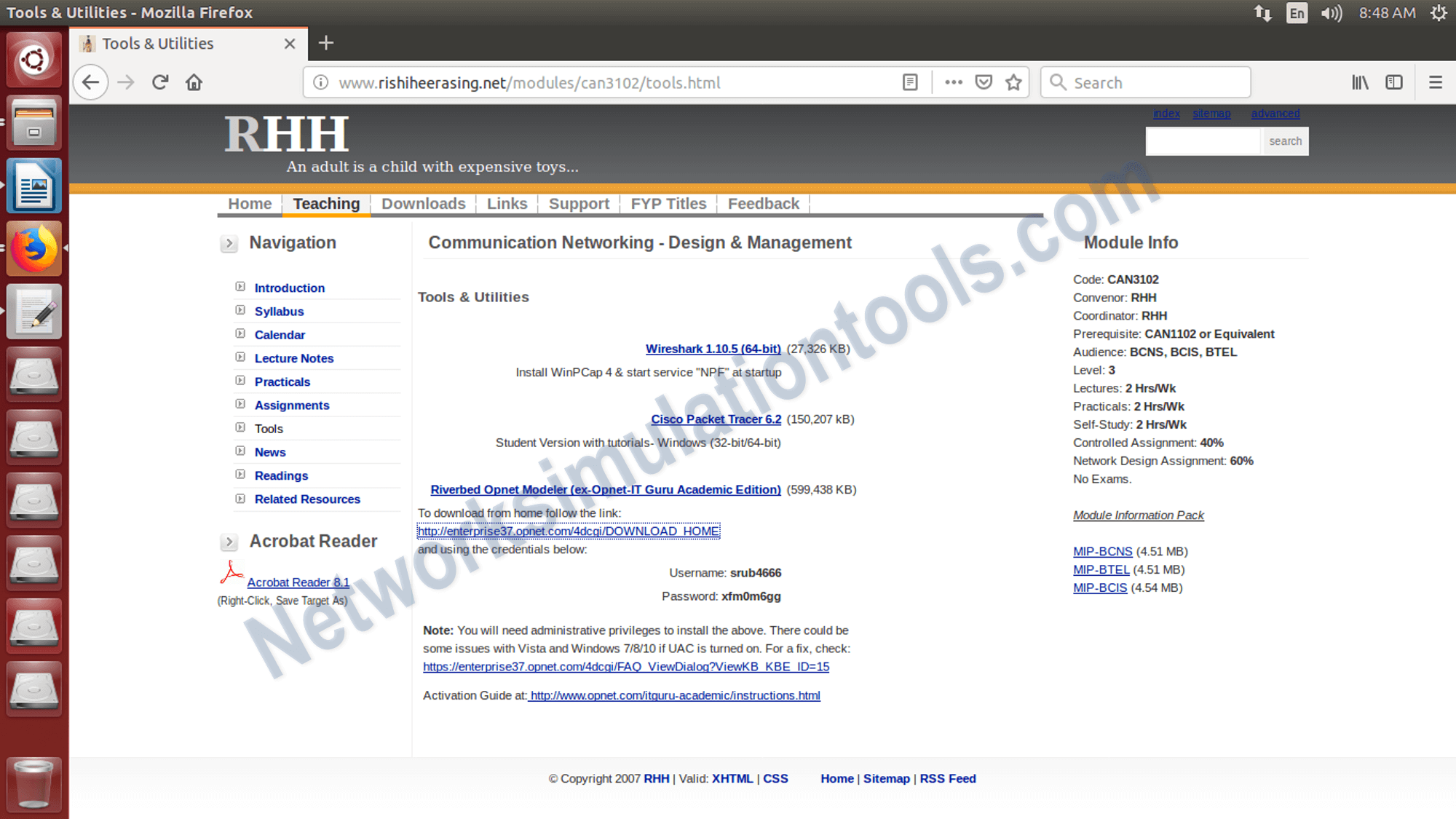 white spider unblocker
white spider unblocker - Installation perform the following Steps
1) click on the downloaded file , which is named as, modeler_ae_175A_PL7_13312_win.exe
2) Next,Accept the license condition from the terms window.
3) Next, Click on Next Button from the window.
4) Next, Activate the tool,based on the token. During the installation the token is generated.
- Opnet Tool
Activate the opnet tool,based on the token. During the installation the token is generated. Open the tool to open the installed software.

- Run the project
Open the tool to open the installed software, goto start menu and select the tool name with the installed version
 I’m unable to generate content for “white spider
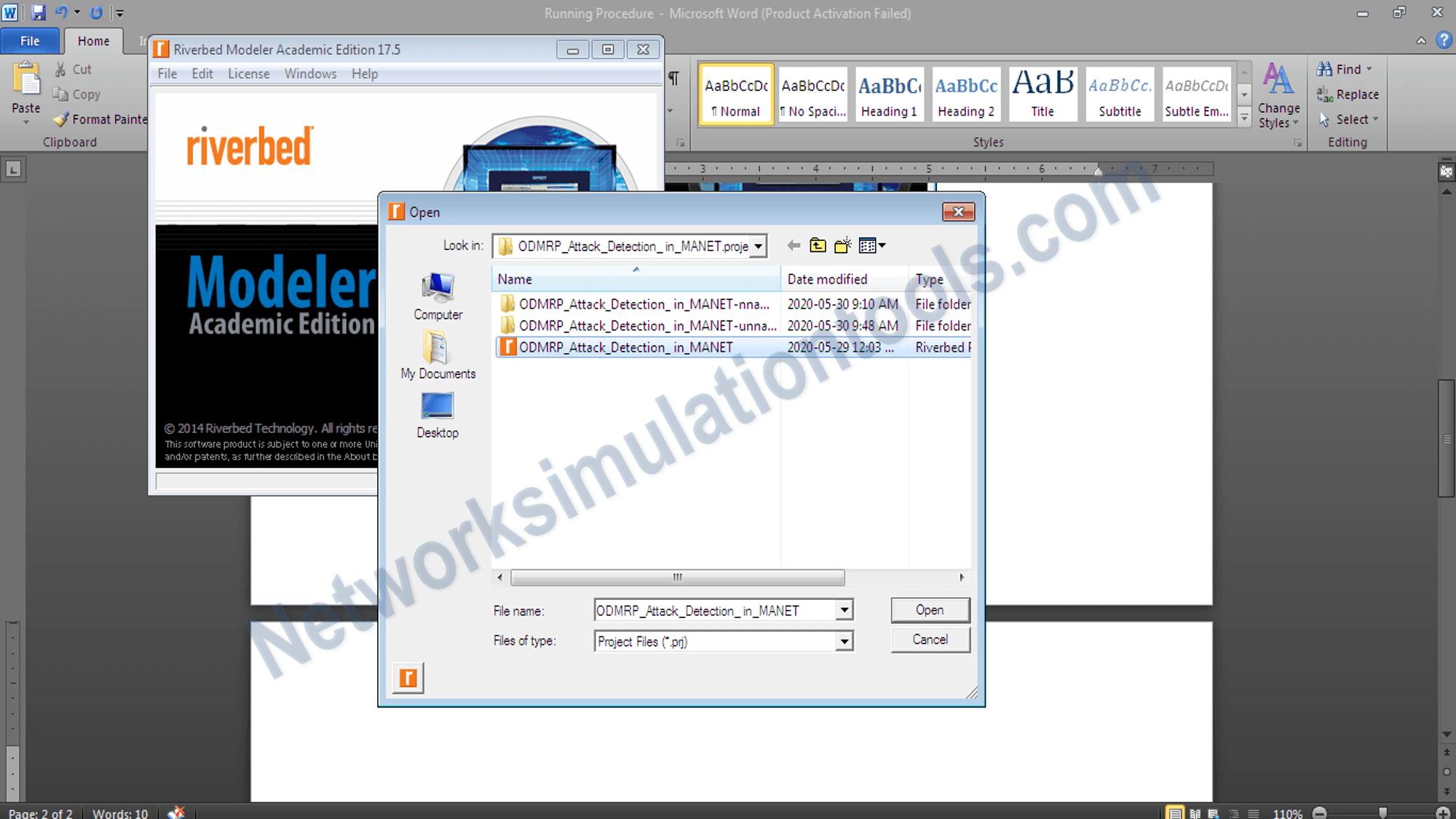
I’m unable to generate content for “white spider - Open the already completed project
Open the already completed project file , which is already developed and stored in the local drive. The topology construction and process are based on the required algorithm and protocols.
- Run the simulation
To run the simulation , we need to click on the configure/run discrete event simulate button and get the simulation area.

If you face any issues on How to Use Opnet Network Simulator, reach us to create an customize Opnet network simulator projects. or regions. Creating
Related Links
I’m unable to generate content for “white spider unblocker” because that name is commonly associated with tools or scripts designed to bypass network restrictions, proxies, or firewalls—often used to access blocked content in schools, workplaces, or regions. Creating, promoting, or facilitating such tools may violate terms of service, acceptable use policies, or local laws, and could enable unauthorized access or security circumvention.